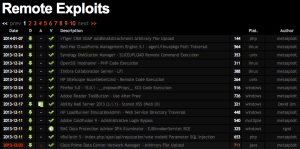
Repositorio Exploit-DB
En una auditoría de seguridad, uno de los objetivos puede ser vulnerar cuantas máquinas sean posibles. Para ello, nos valdremos de distintas herramientas escaneadores de red y puertos como nmap, visualizador y capturador de tráfico como Wireshark, alguna tool para hacer ataques MITM, como Cain y Abel y Evil FOCA etc..
Y para la parte de explotación, lo mas probable es que acabemos escogiendo Metasploit como Framework, pero no nos olvidemos que TODO no está en Metasploit.
Cuando detectamos una vulnerabilidad y queremos saber si hay un Exploit disponible, lo mas seguro es que vayamos a páginas como Exploit-DB para buscar la versión vulnerable.
La gente de Exploit-DB ha colgado todos los exploits en Github por lo que ahora has de actualizar el repositorio y con un script hacer la búsqueda necesaria.
Para bajar el repositorio hacemos:
git clone https://github.com/offensive-security/exploit-database.git
Antes de buscar nada, voy a ver si hay cambios.
seifreed@blackhole:~/tools/pentest/exploit-database$ git pull remote: Counting objects: 18, done. remote: Compressing objects: 100% (4/4), done. remote: Total 8 (delta 4), reused 8 (delta 4) Unpacking objects: 100% (8/8), done. From https://github.com/offensive-security/exploit-database 9819ace..06a2c0f master -> origin/master * [new tag] 01132014 -> 01132014 Updating 9819ace..06a2c0f Fast-forward files.csv | 1 + platforms/php/webapps/30357.txt | 66 ++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++ 2 files changed, 67 insertions(+) create mode 100755 platforms/php/webapps/30357.txt
Y ahora lo que haremos ver como funciona el script de búsqueda:
#!/bin/bash
# exploitdb CLI search tool
csvpath=/usr/share/exploitdb/files.csv
USAGE="Usage: `basename $0` [term1] [term2] [term3]\nExample: `basename $0` oracle windows local\n\nUse lower case in the search terms; second and third terms are optional.
\n`basename $0` will search each line of the csv file left to right so order your search terms accordingly.\n(ie: 'oracle local' will yield better results than 'local oracle')"
if [ $# -eq 0 ]; then
echo -e $USAGE >&2
exit 1
fi
echo " Description Path"
echo --------------------------------------------------------------------------- -------------------------
awk -F "\"*,\"*" '{printf "%-75s %s\n", $3, $2}' $csvpath | awk 'tolower($0) ~ /'$1'/ && /'$2'/ && /'$3'/' | sed s/platforms//
# You can change the identation on the path by changing the "75" above to something that suits your fancy
# (ie: screen columns) 75 columns seemed a good compromise, a few lines will get truncated, but hey...
# ideas and threats: [email protected], backtrack forums or find me at freenode (sygo).
<span style="line-height: 1.5em;">
Como veis, el script de búsqueda, busca en un path, por lo que tendremos que modificarlo para adaptarlo a nuestras necesidades.
Una vez que lo hemos modificado solo tendremos que hacer las búsquedas correctas :
Como ejemplo:
seifreed@blackhole:~/tools/pentest/exploit-database$ sh searchsploit windows local Description Path --------------------------------------------------------------------------- ------------------------- MS Windows XP (explorer.exe) Buffer Overflow Exploit /windows/local/32.c ICQ Pro 2003a Password Bypass exploit (ca1-icq.asm) /windows/local/52.asm DameWare Mini Remote Control Server SYSTEM Exploit /windows/local/79.c MS Windows (ListBox/ComboBox Control) Local Exploit (MS03-045) /windows/local/122.c FirstClass Desktop 7.1 (latest) Buffer Overflow Exploit /windows/local/172.c MS Windows Utility Manager Local SYSTEM Exploit (MS04-011) /windows/local/271.c WinZIP MIME Parsing Overflow Proof of Concept Exploit /windows/local/272.c MS Windows 2000 Utility Manager Privilege Elevation Exploit (MS04-019) /windows/local/350.c MS Windows 2K POSIX Subsystem Privilege Escalation Exploit (MS04-020) /windows/local/351.c MS Windows 2000 Universal Language Utility Manager Exploit (MS04-019) /windows/local/352.c MS Windows 2K/XP Task Scheduler .job Exploit (MS04-022) /windows/local/353.c MS Windows 2k Utility Manager (All-In-One) Exploit (MS04-019) /windows/local/355.c MS Windows XP Task Scheduler (.job) Universal Exploit (MS04-022) /windows/local/368.c Serv-U 3x - 5.x Local Privilege Escalation Exploit /windows/local/381.c Ollydbg <= 1.10 Format String Bug /windows/local/388.c AOL Instant Messenger AIM ""Away"" Message Local Exploit /windows/local/395.c IPSwitch IMail Server <= 8.1 - Local Password Decryption Utility /windows/local/401.c IPD (Integrity Protection Driver) Local Exploit /windows/local/403.c WinRAR 1.0 - Local Buffer Overflow Exploit /windows/local/558.c Zinf 2.2.1 - Local Buffer Overflow Exploit /windows/local/559.c GlobalSCAPE - CuteFTP macros (.mcr) - Local Vulnerability /windows/local/560.txt WinRAR <= 3.4.1 Corrupt ZIP File Vulnerability PoC /windows/local/694.c MS Windows Improper Token Validation Local Exploit (working) /windows/local/749.cpp Peer2Mail <= 1.4 Encrypted Password Dumper Exploit /windows/local/760.cpp Funduc Search and Replace Compressed File Local BoF Exploit /windows/local/769.c DelphiTurk CodeBank 3.1 - Local Username and Password Disclosure /windows/local/798.c DelphiTurk FTP 1.0 - Passwords to Local Users Exploit /windows/local/803.c DelphiTurk e-Posta 1.0 - Local Exploit /windows/local/811.c PeerFTP 5 Local Password Disclosure Exploit /windows/local/833.cpp eXeem 0.21 Local Password Disclosure Exploit /windows/local/834.c SendLink 1.5 - Local Password Disclosure Exploit /windows/local/835.c WWW File Share Pro 2.72 Local Password Disclosure Exploit /windows/local/836.c Chat Anywhere 2.72a Local Password Disclosure Exploit /windows/local/837.c Avaya IP Office Phone Manager Local Password Disclosure Exploit /windows/local/839.cpp eXeem 0.21 Local Password Disclosure Exploit (asm) /windows/local/844.asm Einstein <= 1.01 Local Password Disclosure Exploit /windows/local/846.cpp Einstein <= 1.01 Local Password Disclosure Exploit (asm) /windows/local/848.asm RealPlayer 10 "".smil"" File Local Buffer Overflow Exploit /windows/local/863.cpp iSnooker <= 1.6.8 - Local Password Disclosure Exploit /windows/local/884.cpp iPool <= 1.6.81 Local Password Disclosure Exploit /windows/local/885.cpp BakBone NetVault 6.x/7.x Local Stack Buffer Overflow Exploit /windows/local/905.c GetDataBack Data Recovery 2.31 - Local Exploit /windows/local/912.c FTP Now <= 2.6.14 Local Password Disclosure Exploit /windows/local/918.c FireFly 1.0 - Local Proxy Password Disclosure Exploit /windows/local/919.c P2P Share Spy 2.2 - Local Password Disclosure Exploit /windows/local/920.c MS Jet Database (msjet40.dll) DB File Buffer Overflow Exploit /windows/local/927.c MS Jet Database (msjet40.dll) Reverse Shell Exploit /windows/local/929.py Oracle Database Server <= 10.1.0.2 - Buffer Overflow Exploit /windows/local/932.sql Oracle Database PL/SQL Statement Multiple SQL Injection Exploits /windows/local/933.sql Morpheus <= 4.8 - Local Chat Passwords Disclosure Exploit /windows/local/935.c DeluxeFtp 6.x Local Password Disclosure Exploit /windows/local/936.c BitComet 0.57 Local Proxy Password Disclosure Exploit /windows/local/937.c MS Windows (HTA) Script Execution Exploit (MS05-016) /windows/local/938.cpp MS Jet Database (msjet40.dll) Reverse Shell Exploit /windows/local/951.py GoText 1.01 Local User Informations Disclosure Exploit /windows/local/963.c FilePocket 1.2 - Local Proxy Password Disclosure Exploit /windows/local/964.c ICUII 7.0 - Local Password Disclosure Exploit /windows/local/965.c NotJustBrowsing 1.0.3 - Local Password Disclosure Exploit /windows/local/966.c BulletProof FTP Server 2.4.0.31 Local Privilege Escalation Exploit /windows/local/971.cpp MS Windows COM Structured Storage Local Exploit (MS05-012) /windows/local/1019.c Kaspersky AntiVirus ""klif.sys"" Privilege Escalation Vulnerability /windows/local/1032.cpp WinZIP <= 8.1 Command Line Local Buffer Overflow Exploit /windows/local/1034.cpp Willing Webcam 2.8 Licence Info Disclosure Local Exploit /windows/local/1085.c Access Remote PC 4.5.1 - Local Password Disclosure Exploit /windows/local/1086.c Internet Download Manager <= 4.05 Input URL Stack Overflow Exploit /windows/local/1091.c MS Windows (LegitCheckControl.dll) Genuine Advantage Validation Patch /windows/local/1128.c BakBone NetVault 7.1 - Local Privilege Escalation Exploit /windows/local/1161.c WinAce 2.6.0.5 Temporary File Parsing Buffer Overflow Vulnerability /windows/local/1168.c Mercora IMRadio <= 4.0.0.0 - Local Password Disclosure Exploit /windows/local/1173.c ZipTorrent <= 1.3.7.3 - Local Proxy Password Disclosure Exploit /windows/local/1174.c MS Windows (keybd_event) Local Privilege Elevation Exploit /windows/local/1197.c MS Windows CSRSS Local Privilege Escalation Exploit (MS05-018) /windows/local/1198.c WinRAR 3.30 Long Filename Buffer Overflow Exploit /windows/local/1403.c WinRAR 3.30 Long Filename Buffer Overflow Exploit (more targets) (2) /windows/local/1404.c PHP <= 4.4.0 (mysql_connect function) Local Buffer Overflow Exploit /windows/local/1406.php MS Windows 2k Kernel APC Data-Free Local Escalation Exploit (MS05-055) /windows/local/1407.c Oracle Database Server 9i/10g (XML) Buffer Overflow Exploit /windows/local/1455.txt MS Windows Services ACLs Local Privilege Escalation Exploit (updated) /windows/local/1465.c Microsoft HTML Help Workshop (.hhp file) Buffer Overflow Exploit /windows/local/1470.c Microsoft HTML Help Workshop (.hhp file) Buffer Overflow Exploit (new) /windows/local/1490.c Microsoft HTML Help Workshop (.hhp file) Buffer Overflow Exploit (3) /windows/local/1495.cpp MS Visual Studio 6.0 sp6 (Malformed .dbp File) Buffer Overflow Exploit /windows/local/1555.c MS Windows Telephony Service Command Execution Exploit (MS05-040) /windows/local/1584.cpp Intel Wireless Service (s24evmon.exe) Shared Memory Exploit /windows/local/1772.c IntelliTamper 2.07 - (.map file) Local Arbitrary Code Execution Exploit /windows/local/1806.c MS Windows (NtClose DeadLock) Vulnerability PoC (MS06-030) /windows/local/1910.c MS Windows XP/2K (Mrxsmb.sys) Privilege Escalation PoC (MS06-030) /windows/local/1911.c Pico Zip 4.01 (Long Filename) Buffer Overflow Exploit /windows/local/1917.pl Microsoft Excel Unspecified Remote Code Execution Exploit /windows/local/1944.c Microsoft Excel 2003 Hlink Stack/SEH Buffer Overflow Exploit /windows/local/1958.pl Microsoft Excel Universal Hlink Local Buffer Overflow Exploit /windows/local/1978.pl WinRAR <= 3.60 beta 6 (SFX Path) Local Stack Overflow Exploit /windows/local/1985.py Microsoft Excel 2000/2003 Hlink Local Buffer Overflow Exploit (french) /windows/local/1986.cpp Microsoft Excel 2003 Hlink Local Buffer Overflow Exploit (italian) /windows/local/1988.pl WinRAR <= 3.60 beta 6 (SFX Path) Local Stack Overflow Exploit (french) /windows/local/1992.py Microsoft Word 2000/2003 Hlink Local Buffer Overflow Exploit PoC /windows/local/1999.pl Microsoft IIS ASP Stack Overflow Exploit (MS06-034) /windows/local/2056.c Cheese Tracker <= 0.9.9 - Local Buffer Overflow Exploit PoC /windows/local/2065.c Microsoft PowerPoint 2003 SP2 Local Code Execution Exploit (french) /windows/local/2091.cpp Open Cubic Player <= 2.6.0pre6 / 0.1.10_rc5 Multiple BOF Exploit /windows/local/2094.c VMware 5.5.1 (ActiveX) Local Buffer Overflow Exploit /windows/local/2264.htm ZipCentral 4.01 ZIP File Handling Local Buffer Overflow Exploit /windows/local/2278.cpp TIBCO Rendezvous <= 7.4.11 Password Extractor Local Exploit /windows/local/2284.c PowerZip <= 7.06.3895 Long Filename Handling Buffer Overflow Exploit /windows/local/2286.cpp MS Windows (Windows Kernel) Privilege Escalation Exploit (MS06-049) /windows/local/2412.c Kaspersky Internet Security 6.0.0.303 IOCTL KLICK Local Exploit /windows/local/2676.cpp XMPlay 3.3.0.4 (M3U Filename) Local Buffer Overflow Exploit /windows/local/2815.c XMPlay 3.3.0.4 (ASX Filename) Local Buffer Overflow Exploit /windows/local/2824.c VUPlayer <= 2.44 - (.M3U UNC Name) Buffer Overflow Exploit (c) /windows/local/2872.c AtomixMP3 <= 2.3 - (.M3U) Buffer Overflow Exploit /windows/local/2873.c BlazeVideo HDTV Player <= 2.1 Malformed PLF Buffer Overflow PoC /windows/local/2880.c DeepBurner 1.8.0 .dbr File Parsing Buffer Overflow Exploit /windows/local/2950.c MS Windows NtRaiseHardError Csrss.exe Memory Disclosure Exploit /windows/local/3024.c Microsoft Vista (NtRaiseHardError) Privilege Escalation Exploit /windows/local/3071.c Kaspersky Antivirus 6.0 - Local Privilege Escalation Exploit /windows/local/3131.c Microsoft Help Workshop 4.03.0002 (.CNT) Buffer Overflow Exploit /windows/local/3149.cpp Microsoft Help Workshop 4.03.0002 (.HPJ) Buffer Overflow Exploit /windows/local/3159.cpp Microsoft Visual C++ (.RC Resource Files) Local Buffer Overflow Exploit /windows/local/3176.cpp Multiple Printer Providers (spooler service) - Privilege Escalation Exploit /windows/local/3220.c Microsoft Word 2000 Unspecified Code Execution Exploit (0day) /windows/local/3260.txt News Rover 12.1 Rev 1 Remote Stack Overflow Exploit /windows/local/3342.c News Bin Pro 5.33 (.NBI File) Local Buffer Overflow Exploit /windows/local/3349.c News Rover 12.1 Rev 1 Remote Stack Overflow Exploit (perl) /windows/local/3369.pl PHP <= 4.4.6 mssql_[p]connect() Local Buffer Overflow Exploit /windows/local/3417.php PHP COM extensions (inconsistent Win32) safe_mode Bypass Exploit /windows/local/3429.php PHP 4.4.6 crack_opendict() Local Buffer Overflow Exploit PoC /windows/local/3431.php PHP 4.4.6 snmpget() object id Local Buffer Overflow Exploit PoC /windows/local/3439.php Oracle 10g (PROCESS_DUP_HANDLE) Local Privilege Elevation (win32) /windows/local/3451.c PHP <= 4.4.6 ibase_connect() Local Buffer Overflow Exploit /windows/local/3488.php PHP 5.2.1 with PECL phpDOC Local Buffer Overflow Exploit /windows/local/3576.php Corel Wordperfect X3 13.0.0.565 (.PRS) Local Buffer Overflow Exploit /windows/local/3593.c MS Windows Animated Cursor (.ANI) Stack Overflow Exploit /windows/local/3617.cpp MS Windows Animated Cursor (.ANI) Local Buffer Overflow Exploit /windows/local/3647.c IrfanView 3.99 (.ANI File) Local Buffer Overflow Exploit /windows/local/3648.c Ipswitch WS_FTP 5.05 Server Manager Local Site Buffer Overflow Exploit /windows/local/3649.c MS Windows Animated Cursor (.ANI) Overflow Exploit (Hardware DEP) /windows/local/3652.c TrueCrypt 4.3 - Privilege Escalation Exploit /windows/local/3664.txt MS Windows GDI Local Privilege Escalation Exploit (MS07-017) /windows/local/3688.c IrfanView 3.99 .ANI File Local Buffer Overflow Exploit (multiple targets) /windows/local/3692.c MS Windows Animated Cursor (.ANI) Local Overflow Exploit /windows/local/3695.c VCDGear <= 3.56 Build 050213 (FILE) Local Code Execution Exploit /windows/local/3727.c MS Windows GDI Local Privilege Escalation Exploit (MS07-017) 2 /windows/local/3755.c OllyDbg 1.10 Local Format String Exploit /windows/local/3757.txt Photofiltre Studio 8.1.1 - (.TIF File) Local Buffer Overflow Exploit /windows/local/3772.c ACDSee 9.0 (.XPM File) Local Buffer Overflow Exploit /windows/local/3776.c XnView 1.90.3 (.XPM File) Local Buffer Overflow Exploit /windows/local/3777.c Corel Paint Shop Pro Photo 11.20 (.CLP File) Buffer Overflow Exploit /windows/local/3779.c Adobe Photoshop CS2 / CS3 Unspecified .BMP File Buffer Overflow Exploit /windows/local/3793.c ABC-View Manager 1.42 (.PSP File) Buffer Overflow Exploit /windows/local/3797.c FreshView 7.15 (.PSP File) Buffer Overflow Exploit /windows/local/3798.c Gimp 2.2.14 .RAS File SUNRAS Plugin Buffer Overflow Exploit /windows/local/3801.c IrfanView <= 4.00 .IFF File Buffer Overflow Exploit /windows/local/3811.c Photoshop CS2/CS3 / Paint Shop Pro 11.20 .PNG File BoF Exploit /windows/local/3812.c Winamp <= 5.34 .MP4 File Code Execution Exploit /windows/local/3823.c East Wind Software (advdaudio.ocx 1.5.1.1) Local BoF Exploit /windows/local/3856.htm Gimp 2.2.14 .RAS File Download/Execute Buffer Overflow Exploit (win32) /windows/local/3888.c eTrust Antivirus Agent r8 Local Privilege Elevation Exploit /windows/local/3897.c notepad++ 4.1 ruby file processing Buffer Overflow Exploit (win32) /windows/local/3912.c MagicISO <= 5.4 (build239) .cue File Local Buffer Overflow Exploit /windows/local/3975.c UltraISO <= 8.6.2.2011 (Cue/Bin Files) Local Buffer Overflow Exploit /windows/local/4001.cpp UltraISO <= 8.6.2.2011 (Cue/Bin Files) Local Buffer Overflow Exploit 2 /windows/local/4002.py DVD X Player 4.1 Professional .PLF file Buffer Overflow Exploit /windows/local/4024.rb MoviePlay 4.76 .lst File Local Buffer Overflow Exploit /windows/local/4051.rb PHP 5.2.3 Tidy extension Local Buffer Overflow Exploit /windows/local/4080.php WinPcap 4.0 NPF.SYS Privilege Elevation Vulnerability PoC Exploit /windows/local/4165.c Symantec AntiVirus symtdi.sys Local Privilege Escalation Exploit /windows/local/4178.txt PHP <= 5.2.3 snmpget() object id Local Buffer Overflow Exploit /windows/local/4204.php PHP 5.2.3 win32std ext. safe_mode/disable_functions Protections Bypass /windows/local/4218.php CrystalPlayer 1.98 - (.mls) Local Buffer Overflow Exploit /windows/local/4229.pl PHP 5.x (win32service) Local Safe Mode Bypass Exploit /windows/local/4236.php Live for Speed S1/S2/Demo (.mpr replay file) Buffer Overflow Exploit /windows/local/4252.c Panda Antivirus 2008 Local Privilege Escalation Exploit /windows/local/4257.c Live for Speed S1/S2/Demo (.ply file) Buffer Overflow Exploit /windows/local/4262.cpp Live for Speed S1/S2/Demo (.spr file) Buffer Overflow Exploit /windows/local/4263.cpp PHP mSQL (msql_connect) Local Buffer Overflow Exploit /windows/local/4270.php PHP <= 5.2.3 snmpget() object id Local Buffer Overflow Exploit (EDI) /windows/local/4274.php PHP <= 5.2.3 (php_win32sti) Local Buffer Overflow Exploit /windows/local/4302.php PHP <= 5.2.3 (php_win32sti) Local Buffer Overflow Exploit (2) /windows/local/4303.php PHP FFI Extension 5.0.5 - Local Safe_mode Bypass Exploit /windows/local/4311.php PHP Perl Extension Safe_mode BypassExploit /windows/local/4314.php XAMPP for Windows 1.6.3a Local Privilege Escalation Exploit /windows/local/4325.php Norman Virus Control nvcoaft51.sys ioctl BF672028 Exploit /windows/local/4345.c Virtual DJ 5.0 (m3u File) Local Buffer OverFlow Exploit /windows/local/4354.py OTSTurntables 1.00 (m3u File) Local Buffer Overflow Exploit /windows/local/4355.php Microsoft Visual Basic 6.0 VBP_Open OLE Local CodeExec Exploit /windows/local/4361.pl AtomixMP3 2.3 (pls File) Local Buffer OverFlow Exploit /windows/local/4364.php Microsoft Visual Basic Enterprise Edition 6.0 SP6 Code Execution Exploit /windows/local/4431.py PHP 5.2.4 ionCube extension safe_mode / disable_functions Bypass /windows/local/4517.php jetAudio 7.x (m3u File) Local SEH Overwrite Exploit /windows/local/4531.py PHP 5.x COM functions safe_mode and disable_function bypass /windows/local/4553.php Sony CONNECT Player 4.x (m3u File) Local Stack Overflow Exploit /windows/local/4583.py Kodak Image Viewer TIF/TIFF Code Execution Exploit PoC (MS07-055) /windows/local/4584.c Microsoft Jet Engine MDB File Parsing Stack Overflow PoC /windows/local/4625.txt Media Player Classic 6.4.9 MP4 File Stack Overflow Exploit /windows/local/4701.pl Windows Media Player 6.4 MP4 File Stack Overflow PoC /windows/local/4702.pl Nullsoft Winamp 5.32 MP4 tags Stack Overflow Exploit /windows/local/4703.pl Rosoft Media Player <= 4.1.7 .M3U Stack Overflow Exploit /windows/local/4749.c jetAudio 7.0.5 COWON Media Center MP4 Stack Overflow Exploit /windows/local/4751.pl CoolPlayer 2.17 .m3u Playlist Stack Overflow Exploit /windows/local/4839.pl Microsoft Visual InterDev 6.0 (SP6) .sln File Local Buffer Overflow Exploit /windows/local/4892.py MS Visual Basic Enterprise Ed. 6 SP6 .dsr File Handling BOF Exploit /windows/local/4938.py IrfanView 4.10 .FPX File Memory Corruption Exploit /windows/local/4998.c Safenet IPSecDrv.sys <= 10.4.0.12 Local kernel ring0 SYSTEM Exploit /windows/local/5004.c Total Video Player 1.03 M3U File Local Buffer Overflow Exploit /windows/local/5032.c Total Video Player 1.20 M3U File Local Stack Buffer Overflow Exploit /windows/local/5077.cpp Microsoft Office .WPS File Stack Overflow Exploit (MS08-011) /windows/local/5107.c DESlock+ <= 3.2.6 (list) Local Kernel Memory Leak PoC /windows/local/5141.c DESlock+ <= 3.2.6 - Local Kernel ring0 link list zero SYSTEM Exploit /windows/local/5143.c DESlock+ <= 3.2.6 DLMFDISK.sys local kernel ring0 SYSTEM Exploit /windows/local/5144.c VLC <= 0.8.6e Subtitle Parsing Local Buffer Overflow Exploit /windows/local/5250.cpp Microsoft Office Excel Code Execution Exploit (MS08-014) /windows/local/5287.txt Microsoft Office XP SP3 PPT File Buffer Overflow Exploit (ms08-016) /windows/local/5320.txt XnView 1.92.1 Slideshow (FontName) Buffer Overflow Exploit /windows/local/5346.pl MS Visual Basic Enterprise Ed. 6 SP6 DSR File Local BOF Exploit /windows/local/5361.py MS Windows GDI Image Parsing Stack Overflow Exploit (MS08-021) /windows/local/5442.cpp DivX Player 6.6.0 SRT File SEH Buffer Overflow Exploit /windows/local/5462.py Adobe Album Starter 3.2 Unchecked Local Buffer Overflow Exploit /windows/local/5479.txt DivX Player 6.7 SRT File Subtitle Parsing Buffer Overflow Exploit /windows/local/5492.cpp Kantaris 0.3.4 SSA Subtitle Local Buffer Overflow Exploit /windows/local/5498.py MS Windows XP SP2 (win32k.sys) Privilege Escalation Exploit (MS08-025) /windows/local/5518.txt Open Office.org 2.31 swriter Local Code Execution Exploit /windows/local/5584.c Symantec Altiris Client Service 6.8.378 Local Privilege Escalation Exploit /windows/local/5625.c VLC 0.8.6d SSA Parsing Double Sh311 Universal Exploit /windows/local/5667.py Deterministic Network Enhancer dne2000.sys kernel ring0 SYSTEM exploit /windows/local/5837.c XnView 1.93.6 for Windows .taac Local Buffer Overflow Exploit PoC /windows/local/5951.c Download Accelerator Plus - DAP 8.x (m3u) Local BOF Exploit 0day /windows/local/6030.py OllyDBG 1.10 and ImpREC 1.7f - (export name) BOF PoC /windows/local/6031.asm Download Accelerator Plus - DAP 8.x m3u File Buffer Overflow Exploit (c) /windows/local/6039.c IntelliTamper 2.07 (map file) Local Arbitrary Code Execution Exploit (pl) /windows/local/6106.pl CoolPlayer m3u File Local Buffer Overflow Exploit /windows/local/6157.pl IrfanView <= 3.99 IFF File Local Stack Buffer Overflow Exploit /windows/local/6188.c Acoustica Mixcraft <= 4.2 Build 98 (mx4 file) Local BOF Exploit /windows/local/6322.pl Acoustica MP3 CD Burner 4.51 Build 147 (asx file) Local BOF Exploit /windows/local/6329.pl Acoustica Beatcraft 1.02 Build 19 (bcproj file) Local BOF Exploit /windows/local/6333.pl Numark Cue 5.0 rev 2 Local .M3U File Stack Buffer Overflow Exploit /windows/local/6389.cpp MS Windows 2003 Token Kidnapping Local Exploit PoC /windows/local/6705.txt MS Windows XP/2003 AFD.sys Privilege Escalation Exploit (K-plugin) /windows/local/6757.txt BitTorrent 6.0.3 .torrent File Stack Buffer Overflow Exploit /windows/local/6787.pl VLC Media Player TY File Stack Based Buffer Overflow Exploit /windows/local/6798.pl VLC 0.9.4 .TY File Buffer Overflow Exploit (SEH) /windows/local/6825.pl TUGzip 3.00 archiver .ZIP File Local Buffer Overflow Exploit /windows/local/6831.cpp Adobe Reader util.printf() JavaScript Function Stack Overflow Exploit /windows/local/6994.txt Adobe Reader util.printf() JavaScript Function Stack Overflow Exploit #2 /windows/local/7006.txt VLC Media Player < 0.9.6 .RT Stack Buffer Overflow Exploit /windows/local/7051.pl Anti-Keylogger Elite 3.3.0 (AKEProtect.sys) Privilege Escalation Exploit /windows/local/7054.txt Opera 9.62 file:// Local Heap Overflow Exploit /windows/local/7135.htm Apache Tomcat runtime.getRuntime().exec() Privilege Escalation (win) /windows/local/7264.txt Cain & Abel <= 4.9.24 - .RDP Stack Overflow Exploit /windows/local/7309.pl Cain & Abel 4.9.23 (rdp file) Buffer overflow Exploit /windows/local/7329.py RadAsm <= 2.2.1.5 (.RAP File) WindowCallProcA Pointer Hijack Exploit /windows/local/7334.pl PEiD <= 0.92 Malformed PE File Universal Buffer Overflow Exploit /windows/local/7347.pl Realtek Sound Manager (rtlrack.exe 1.15.0.0) - PlayList BOF Exploit /windows/local/7492.py Microsoft SQL Server sp_replwritetovarbin() Heap Overflow Exploit /windows/local/7501.asp ESET Smart Security <= 3.0.672 (epfw.sys) Privilege Escalation Exploit /windows/local/7516.txt PowerStrip < = 3.84 (pstrip.sys) Privilege Escalation Exploit /windows/local/7533.txt CoolPlayer 2.19 (Skin File) Local Buffer Overflow Exploit /windows/local/7536.cpp CoolPlayer 2.19 (Skin File) Local Buffer Overflow Exploit (py) /windows/local/7547.py Acoustica Mixcraft <= 4.2 Universal Stack Overflow Exploit (SEH) /windows/local/7577.pl IntelliTamper 2.07/2.08 (MAP File) Local SEH Overwrite Exploit /windows/local/7582.py IntelliTamper 2.07/2.08 (ProxyLogin) Local Stack Overflow Exploit /windows/local/7608.py Destiny Media Player 1.61 (.m3u File) Local Stack Overflow Exploit /windows/local/7651.py Destiny Media Player 1.61 (lst File) Local Buffer Overflow Exploit /windows/local/7654.pl Destiny Media Player 1.61 (lst File) Local Buffer Overflow Exploit #2 /windows/local/7655.pl Destiny Media Player 1.61 (lst File) Local Buffer Overflow Exploit #3 /windows/local/7656.pl Destiny Media Player 1.61 (lst File) Local Buffer Overflow Exploit #4 /windows/local/7661.pl Destiny Media Player 1.61 (lst File) Local Buffer Overflow Exploit #5 /windows/local/7662.py VUPlayer 2.49 - (.wax File) Local Buffer Overflow Exploit /windows/local/7671.pl Rosoft Media Player 4.2.1 - Local Buffer Overflow Exploit /windows/local/7684.pl Cain & Abel 4.9.25 (Cisco IOS-MD5) Local Buffer Overflow Exploit /windows/local/7688.pl CoolPlayer BUILD 219 (PlaylistSkin) Buffer Overflow Exploit /windows/local/7692.pl VUPlayer <= 2.49 - (.PLS) Universal Buffer Overflow Exploit /windows/local/7695.pl GOM Player 2.0.12.3375 (.ASX File) Stack Overflow Exploit /windows/local/7702.c IntelliTamper (2.07/2.08) Language Catalog SEH Overflow Exploit /windows/local/7707.py VUPlayer 2.49 - .ASX File (HREF) Local Buffer Overflow Exploit (2) /windows/local/7713.pl VUPlayer 2.49 - .ASX File (HREF) Local Buffer Overflow Exploit (1) /windows/local/7714.pl VUPlayer 2.49 - .ASX File (HREF) Universal Buffer Overflow Exploit /windows/local/7715.py Microsoft HTML Workshop <= 4.74 Universal Buffer Overflow Exploit /windows/local/7727.pl VUPlayer 2.49 - .ASX File (Universal) Local Buffer Overflow Exploit /windows/local/7745.py OTSTurntables 1.00.027 (.ofl) Local Stack Overflow Exploit /windows/local/7765.py Total Video Player 1.31 (DefaultSkin.ini) Local Stack Overflow Exploit /windows/local/7839.py Browser3D 3.5 (.sfs File) Local Stack Overflow Exploit (c) /windows/local/7843.c Browser3D 3.5 (.sfs File) Local Stack Overflow Exploit /windows/local/7848.pl EleCard MPEG PLAYER (.m3u file) Local Stack Overflow Exploit /windows/local/7853.pl Zinf Audio Player 2.2.1 (PLS File) Local Buffer Overflow Exploit (univ) /windows/local/7888.pl Total Video Player 1.3.7 (.m3u) Local Buffer Overflow Exploit /windows/local/7923.c GOM Player 2.0.12 (.PLS) Universal Buffer Overflow Exploit /windows/local/7929.c Free Download Manager <= 3.0 Build 844 .torrent BOF Exploit /windows/local/7957.pl Euphonics Audio Player 1.0 - (.pls) Local Buffer Overflow Exploit /windows/local/7958.pl Euphonics Audio Player 1.0 (.pls) Universal Local Buffer Overflow Exploit /windows/local/7973.pl Euphonics Audio Player 1.0 (.pls) Local Buffer Overflow Exploit (xp/sp3) /windows/local/7974.c BlazeVideo HDTV Player <= 3.5 PLF Playlist File Remote Overflow Exploit /windows/local/7975.py dBpowerAMP Audio Player 2 .PLS File Local Buffer Overflow Exploit /windows/local/7994.c FeedDemon <= 2.7 OPML Outline Tag Buffer Overflow Exploit /windows/local/8010.pl Hex Workshop 6.0 - (.HEX File) Local Code Execution Exploit /windows/local/8121.pl Merak Media PLayer 3.2 m3u File Local Buffer Overflow Exploit (SEH) /windows/local/8126.py Media Commands (m3u File) Local SEH Overwrite Exploit /windows/local/8137.py VUplayer 2.49 - .CUE File Local Buffer Overflow Exploit /windows/local/8138.c Winamp <= 5.541 Skin Universal Buffer Overflow Exploit /windows/local/8158.pl Media Commands .m3l File Local Buffer Overflow Exploit /windows/local/8159.rb Media Commands (m3u File) Universal SEH Overwrite Exploit /windows/local/8162.py Nokia Multimedia Player 1.0 (playlist) Universal SEH Overwrite Exploit /windows/local/8171.py Realtek Sound Manager 1.15.0.0 PlayList SEH Overwrite Exploit /windows/local/8174.py mks_vir 9b < 1.2.0.0b297 (mksmonen.sys) Privilege Escalation Exploit /windows/local/8175.txt EO Video 1.36 - PlayList SEH Overwrite Exploit /windows/local/8176.py RadASM 2.2.1.5 (.RAP File) Local Stack Overflow Exploit /windows/local/8177.py MediaCoder 0.6.2.4275 (m3u File) Universal Stack Overflow Exploit /windows/local/8178.pl MediaCoder 0.6.2.4275 Universal Buffer Overflow Exploit (SEH) /windows/local/8179.rb VUPlayer <= 2.49 - (.cue) Universal Buffer Overflow Exploit /windows/local/8189.txt RainbowPlayer 0.91 (playlist) Universal SEH Overwrite Exploit /windows/local/8193.py Foxit Reader 3.0 (<= Build 1301) PDF Buffer Overflow Exploit (Univ.) /windows/local/8201.pl Rosoft Media Player 4.2.1 - Local Buffer Overflow Exploit (multi target) /windows/local/8214.c CDex 1.70b2 (.ogg) Local Buffer Overflow Exploit (xp/ sp3) /windows/local/8231.php Chasys Media Player 1.1 (.pls) Local Stack overflow Exploit /windows/local/8233.py Chasys Media Player 1.1 (.pls) Stack Overflow Exploit #2 /windows/local/8234.py Chasys Media Player 1.1 (.m3u) Stack Overflow Exploit /windows/local/8235.py Icarus 2.0 (.PGN File) Local Stack Overflow Exploit (SEH) /windows/local/8236.py Chasys Media Player 1.1 .cue File Stack Overflow Exploit /windows/local/8242.rb Chasys Media Player (.lst playlist) Local Buffer Overflow Exploit /windows/local/8246.pl BS.Player <= 2.34 Build 980 (.bsl) Local Buffer Overflow Exploit (SEH) /windows/local/8249.php CloneCD/DVD (ElbyCDIO.sys < 6.0.3.2) Local Privilege Escalation Exploit /windows/local/8250.txt BS.Player 2.34 (.bsl) Universal SEH Overwrite Exploit /windows/local/8251.py Zinf Audio Player 2.2.1 (.pls) Universal Seh Overwrite Exploit /windows/local/8267.py eXeScope 6.50 Local Buffer Overflow Exploit /windows/local/8270.pl POP Peeper 3.4.0.0 .eml file Universal SEH Overwrite Exploit /windows/local/8274.pl POP Peeper 3.4.0.0 .html file Universal SEH Overwrite Exploit /windows/local/8275.pl Adobe Acrobat Reader JBIG2 Universal Exploit Bind Shell port 5500 /windows/local/8280.txt Abee Chm Maker 1.9.5 (CMP File) Stack overflow Exploit /windows/local/8299.py PowerCHM 5.7 (hhp) Local Buffer Overflow Exploit /windows/local/8301.pl Abee Chm eBook Creator 2.11 (FileName) Local Stack Overflow Exploit /windows/local/8311.py AtomixMP3 <= 2.3 - (playlist) Universal SEH Overwrite Exploit /windows/local/8312.py Trend Micro Internet Security Pro 2009 Priviliege Escalation PoC /windows/local/8322.txt UltraISO <= 9.3.3.2685 CCD/IMG Universal Buffer Overflow Exploit /windows/local/8343.pl OTSTurntables 1.00.027 (.m3u/.ofl file) Universal BOF Exploit /windows/local/8371.pl HTML Email Creator <= 2.1b668 (html) Local SEH Overwrite Exploit /windows/local/8401.cpp RM Downloader 3.0.0.9 .m3u Universal Stack Overflow Exploit /windows/local/8410.pl WM Downloader 3.0.0.9 .m3u Universal Stack Overflow Exploit /windows/local/8411.c ASX to MP3 Converter 3.0.0.7 .m3u Universal Stack Overflow Exploit /windows/local/8412.pl Mini-stream RM-MP3 Converter 3.0.0.7 .m3u Stack Overflow Exploit /windows/local/8413.pl Mini-stream Ripper 3.0.1.1 .m3u Universal Stack Overflow Exploit /windows/local/8416.pl BulletProof FTP Client 2009 (.bps) Buffer Overflow Exploit (SEH) /windows/local/8420.py Shadow Stream Recorder (.m3u file) Universal Stack Overflow Exploit /windows/local/8426.pl Easy RM to MP3 Converter Universal Stack Overflow Exploit /windows/local/8427.py Star Downloader Free <= 1.45 (.dat) Universal SEH Overwrite Exploit /windows/local/8444.cpp CoolPlayer Portable 2.19.1 (m3u) Buffer Overflow Exploit /windows/local/8519.pl CoolPlayer Portable 2.19.1 (m3u) Buffer Overflow Exploit #2 /windows/local/8520.py CoolPlayer Portable 2.19.1 (Skin) Buffer Overflow Exploit /windows/local/8527.py Destiny Media Player 1.61 (.rdl) Local Buffer Overflow Exploit /windows/local/8535.pl SDP Downloader 2.3.0 (.ASX) Local Buffer Overflow Exploit (SEH) /windows/local/8536.py SDP Downloader 2.3.0 (.ASX) Local Buffer Overflow Exploit (SEH) #2 /windows/local/8540.c Zoom Player Pro 3.30 (.m3u) - File Buffer Overflow Exploit (seh) /windows/local/8541.php Mercury Audio Player 1.21 (.b4s) Local Stack Overflow Exploit /windows/local/8580.py Mercury Audio Player 1.21 (.pls) SEH Overwrite Exploit /windows/local/8582.py Mercury Audio Player 1.21 (.m3u) Local Stack Overflow Exploit /windows/local/8583.py RM Downloader (.smi File) Local Stack Overflow Exploit /windows/local/8589.py Beatport Player 1.0.0.283 (.m3u) Local SEH Overwrite Exploit /windows/local/8590.py Beatport Player 1.0.0.283 (.M3U File) Local Stack Overflow Exploit #2 /windows/local/8591.py Beatport Player 1.0.0.283 (.M3U File) Local Stack Overflow Exploit #3 /windows/local/8592.pl RM Downloader (.smi File) Universal Local Buffer Overflow Exploit /windows/local/8594.pl
Como veis, solo tendríamos que ir al path que toque y escoger el exploit. Se pueden afinar mas las búsquedas esta claro.