Lynis auditando la seguridad de tu sistema *NIX
Lynis auditando la seguridad de tu sistema *NIX, en la instalación de cualquier sistema, ya sea basado en *NIX, Windows, MAC OS X, si va a estar en producción ofreciendo algún servicio, es bueno que se le pasen algunos checks de seguridad para saber como estamos en materia de seguridad. Estas revisiones también se pueden mirar en sistemas que ya estén en producción para ver si nos hemos dejado algo de configurar.
Lynis auditando la seguridad de tu sistema *NIX descargar Lynis
Primero de todo nos bajamos Lynis, lo podemos descargar de la web de Packet Storm
wget http://packetstorm.interhost.co.il/UNIX/scanners/lynis-1.3.3.tar.gz
Lo tenemos que ejecutar con permisos de súper usuario.
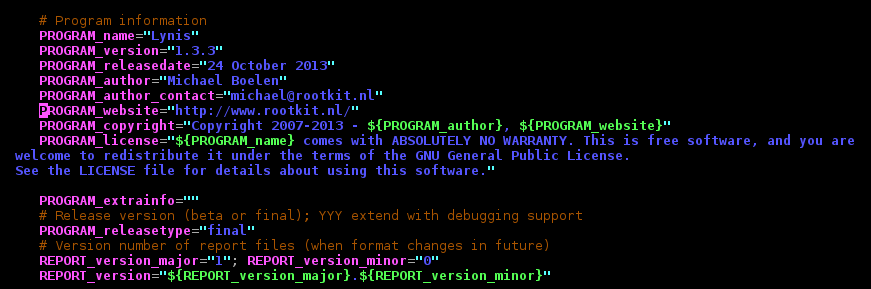
sechelong:/home/ecrime/lynis-1.3.3# ./lynis --check-all [ Lynis 1.3.3 ] ################################################################################ Lynis comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the terms of the GNU General Public License. See the LICENSE file for details about using this software. Copyright 2007-2013 - Michael Boelen, http://www.rootkit.nl/ ################################################################################ [+] Initializing program ------------------------------------ - Detecting OS... [ DONE ] - Clearing log file (/var/log/lynis.log)... [ DONE ] --------------------------------------------------- Program version: 1.3.3 Operating system: Linux Operating system name: Linux Operating system version: 3.2.0-4-amd64 Kernel version: 3.2.0-4-amd64 Hardware platform: x86_64 Hostname: sechelong Auditor: [Unknown] Profile: ./default.prf Log file: /var/log/lynis.log Report file: /var/log/lynis-report.dat Report version: 1.0 ---------------------------------------------------
Primeramente obtenemos un resumen del sistema que vamos a analizar.
- Checking profile file (./default.prf)... - Program update status... [ NO UPDATE ] [+] System Tools ------------------------------------ - Scanning available tools... - Checking system binaries... - Checking /bin... [ FOUND ] - Checking /sbin... [ FOUND ] - Checking /usr/bin... [ FOUND ] - Checking /usr/sbin... [ FOUND ] - Checking /usr/local/bin... [ FOUND ] - Checking /usr/local/sbin... [ FOUND ] - Checking /usr/local/libexec... [ NOT FOUND ] - Checking /usr/libexec... [ NOT FOUND ] - Checking /usr/sfw/bin... [ NOT FOUND ] - Checking /usr/sfw/sbin... [ NOT FOUND ] - Checking /usr/sfw/libexec... [ NOT FOUND ] - Checking /opt/sfw/bin... [ NOT FOUND ] - Checking /opt/sfw/sbin... [ NOT FOUND ] - Checking /opt/sfw/libexec... [ NOT FOUND ] - Checking /usr/xpg4/bin... [ NOT FOUND ] - Checking /usr/css/bin... [ NOT FOUND ] - Checking /usr/ucb... [ NOT FOUND ]
Ahora chequeará los binarios del sistema.
[+] Boot and services ------------------------------------ - Checking boot loaders - Checking presence GRUB2... [ OK ] - Checking presence LILO... [ NOT FOUND ] - Checking presence YABOOT... [ NOT FOUND ] - Check startup files (permissions)... [ OK ]
En este caso lo que hará será hacer un check de que se usa para el sistema de arranque y también si los archivos de startup son correctos
[+] Kernel ------------------------------------ - Checking default run level... [ 2 ] - Checking CPU support (NX/PAE) CPU supports PAE and NoeXecute [ YES ] - Checking kernel version [ DONE ] - Checking kernel type [ DONE ] - Checking loaded kernel modules [ DONE ] Found 76 active modules - Checking Linux kernel configuration file... [ FOUND ] - Checking core dumps configuration... [ DISABLED ] - Checking setuid core dumps configuration... [ DISABLED ]
También hace checks a nivel de kernel.
[+] Memory and processes ------------------------------------ - Checking /proc/meminfo... [ FOUND ] - Searching for dead/zombie processes... [ OK ] - Searching for IO waiting processes... [ OK ] [ Press [ENTER] to continue, or [CTRL]+C to stop ] [+] Users, Groups and Authentication ------------------------------------ - Search administrator accounts... [ OK ] - Checking consistency of group files (grpck)... [ OK ] - Checking non unique group ID's... [ OK ] - Checking non unique group names... [ OK ] - Checking password file consistency... [ OK ] - Query system users (non daemons)... [ DONE ] - Checking NIS+ authentication support [ NOT ENABLED ] - Checking NIS authentication support [ NOT ENABLED ] - Checking sudoers file [ FOUND ] - Check sudoers file permissions [ OK ] - Checking PAM configuration files (pam.conf) [ FOUND ] - Checking PAM configuration files (pam.d) [ FOUND ] - Checking PAM modules [ FOUND ] - Checking LDAP module in PAM [ NOT FOUND ] - Checking accounts without expire date [ SUGGESTION ] - Checking user password aging [ DISABLED ] - Checking Linux single user mode authentication [ OK ] - Determining default umask - Checking umask (/etc/profile) [ SUGGESTION ] - Checking umask (/etc/login.defs) [ SUGGESTION ] - Checking umask (/etc/init.d/rc) [ SUGGESTION ] - Checking LDAP authentication support [ NOT ENABLED ]
Lynis también comprobará cosas como la memoria, usuarios y grupos del sistema.
[+] Shells ------------------------------------ - Checking shells from /etc/shells... Result: found 6 shells (valid shells: 6). [ Press [ENTER] to continue, or [CTRL]+C to stop ] [+] File systems ------------------------------------ - Checking mount points - Checking /home mount point... [ SUGGESTION ] - Checking /tmp mount point... [ SUGGESTION ] - Checking LVM volume groups... [ FOUND ] - Checking LVM volumes... [ FOUND ] - Checking for old files in /tmp... [ OK ] - Checking /tmp sticky bit... [ OK ] - ACL support root file system... [ ENABLED ] - Checking Locate database... [ FOUND ]
Lynis mirará que shells hay en el sistema además de mirar a nivel de file system si hay algún error.
[+] NFS ------------------------------------ - Check running NFS daemon... [ NOT FOUND ] [ Press [ENTER] to continue, or [CTRL]+C to stop ] [+] Software: name services ------------------------------------ - Checking default DNS search domain... [ NONE ] - Checking /etc/resolv.conf options... [ NONE ] - Searching DNS domain name... [ FOUND ] Domain name: fbd.local - Checking nscd status... [ NOT FOUND ] - Checking BIND status... [ NOT FOUND ] - Checking PowerDNS status... [ NOT FOUND ] - Checking ypbind status... [ NOT FOUND ] [ Press [ENTER] to continue, or [CTRL]+C to stop ] [+] Ports and packages ------------------------------------ - Searching package managers... - Searching dpkg package manager... [ FOUND ] - Querying package manager... - Query unpurged packages... [ FOUND ] [ Press [ENTER] to continue, or [CTRL]+C to stop ] [+] Networking ------------------------------------ - Checking configured nameservers... - Testing nameservers... Nameserver: 8.8.8.8... [ OK ] - Minimal of 2 responsive nameservers... [ WARNING ] - Checking default gateway... [ DONE ] - Checking promiscuous interfaces... [ OK ] - Checking waiting connections... [ OK ] [ Press [ENTER] to continue, or [CTRL]+C to stop ] [+] Printers and Spools ------------------------------------ - Checking cups daemon... [ NOT FOUND ] [ Press [ENTER] to continue, or [CTRL]+C to stop ] [+] Software: e-mail and messaging ------------------------------------ - Checking Exim status... [ RUNNING ] - Checking Postfix status... [ NOT FOUND ] - Checking Qmail smtpd status... [ NOT FOUND ]
Lynis comprobará cosas como las impresoras, sistema de correo, si lo tenemos, la parte de Networking.. EN mi caso me ha sacado un Warning porque no tengo DNS secundario.
ESta herramienta hace otros checks, pero para no ponerlos todos os pongo el report que saca la herramienta. Ya que podremos ver incluso que la herramienta nos da recomendaciones
-[ Lynis 1.3.3 Results ]-
Tests performed: 151
Warnings:
----------------------------
- [16:41:23] Warning: Couldn't find 2 responsive nameservers [test:NETW-2705] [impact:L]
- [16:41:47] Warning: iptables module(s) loaded, but no rules active [test:FIRE-4512] [impact:L]
- [16:43:03] Warning: Root can directly login via SSH [test:SSH-7412] [impact:M]
- [16:43:08] Warning: PHP option register_globals option is turned on, which can be a risk for variable value overwriting [test:PHP-2368] [impact:M]
- [16:43:08] Warning: PHP option expose_php is possibly turned on, which can reveal useful information for attackers. [test:PHP-2372] [impact:M]
- [16:43:17] Warning: No running NTP daemon or available client found [test:TIME-3104] [impact:M]Suggestions:
----------------------------
- [16:39:26] Suggestion: When possible set expire dates for all password protected accounts [test:AUTH-9282]
- [16:39:26] Suggestion: Configure password aging limits to enforce password changing on a regular base [test:AUTH-9286]
- [16:39:26] Suggestion: Default umask in /etc/profile could be more strict like 027 [test:AUTH-9328]
- [16:39:26] Suggestion: Default umask in /etc/login.defs could be more strict like 027 [test:AUTH-9328]
- [16:39:26] Suggestion: Default umask in /etc/init.d/rc could be more strict like 027 [test:AUTH-9328]
- [16:40:09] Suggestion: To decrease the impact of a full /home file system, place /home on a separated partition [test:FILE-6310]
- [16:40:09] Suggestion: To decrease the impact of a full /tmp file system, place /tmp on a separated partition [test:FILE-6310]
- [16:40:59] Suggestion: Disable drivers like USB storage when not used, to prevent unauthorized storage or data theft [test:STRG-1840]
- [16:40:59] Suggestion: Disable drivers like firewire storage when not used, to prevent unauthorized storage or data theft [test:STRG-1846]
- [16:41:19] Suggestion: Purge old/removed packages (6 found) with aptitude purge or dpkg --purge command. This will cleanup old configuration files, cron jobs and startup scripts. [test:PKGS-7346]
- [16:41:23] Suggestion: Check your resolv.conf file and fill in a backup nameserver if possible [test:NETW-2705]
- [16:41:47] Suggestion: Disable iptables kernel module if not used or make sure rules are being used [test:FIRE-4512]
- [16:41:47] Suggestion: Configure a firewall/packet filter to filter incoming and outgoing traffic [test:FIRE-4590]
- [16:43:08] Suggestion: Change the register_globals line to: register_globals = Off [test:PHP-2368]
- [16:43:08] Suggestion: Change the expose_php line to: expose_php = Off [test:PHP-2372]
- [16:43:08] Suggestion: Change the allow_url_fopen line to: allow_url_fopen = Off, to disable downloads via PHP [test:PHP-2376]
- [16:43:15] Suggestion: Add legal banner to /etc/motd, to warn unauthorized users [test:BANN-7122]
- [16:43:15] Suggestion: Add legal banner to /etc/issue, to warn unauthorized users [test:BANN-7126]
- [16:43:15] Suggestion: Add legal banner to /etc/issue.net, to warn unauthorized users [test:BANN-7130]
- [16:43:16] Suggestion: Enable auditd to collect audit information [test:ACCT-9628]
- [16:43:17] Suggestion: Check if any NTP daemon is running or a NTP client gets executed daily, to prevent big time differences and avoid problems with services like kerberos, authentication or logging differences. [test:TIME-3104]
- [16:43:20] Suggestion: Install a file integrity tool [test:FINT-4350]
- [16:43:28] Suggestion: One or more sysctl values differ from the scan profile and could be tweaked [test:KRNL-6000]
- [16:43:33] Suggestion: Harden the system by removing unneeded compilers. This can decrease the chance of customized trojans, backdoors and rootkits to be compiled and installed [test:HRDN-7220]
- [16:43:33] Suggestion: Harden compilers and restrict access to world [test:HRDN-7222]
- [16:43:33] Suggestion: Harden the system by installing one or malware scanners to perform periodic file system scans [test:HRDN-7230]
================================================================================
Files:
- Test and debug information : /var/log/lynis.log
- Report data : /var/log/lynis-report.dat
================================================================================
Hardening index : [50] [########## ]
================================================================================
Tip: Disable all tests which are not relevant or are too strict for the
purpose of this particular machine. This will remove unwanted suggestions
and also boost the hardening index. Each test should be properly analyzed
to see if the related risks can be accepted, before disabling the test.
================================================================================
Lynis 1.3.3
Copyright 2007-2013 - Michael Boelen, http://www.rootkit.nl/
================================================================================Una buena herramienta para incluir en checks
Lynis auditando la seguridad de tu sistema *NIX, como veis, es una buena herramienta para incluir en nuestros checks de seguridad de nuestros servidores.